What Is B2C Marketing?
B2C marketing refers to the approach businesses take to directly sell products and services to consumers. This method involves utilizing targeted digital campaigns, personalized communication, and active social media engagement, with a focus on addressing personal needs and interests to effectively drive sales.
The Difference Between B2C vs. B2B
In simple terms, B2C companies sell directly to consumers. Think retail, consumer tech, and the hospitality industry. B2B companies on the other hand sell to other businesses. This would include managed services companies, enterprise software, agencies, and consultants.
Some of the most important distinctions when it comes to B2C vs B2B marketing relate to purchasing and sales processes, decision-makers involved, and cost of purchases.
While a business will likely conduct extensive research before investing in new software, office space, or a large acquisition with another business, B2C transactions are frequently more impulsive and instantaneous.
Consumers generally seek out goods and services based on an immediate need, and make purchases faster, with less research and due diligence than a business would conduct. This grants B2C marketers a much smaller window of opportunity to influence consumer behavior.
For these reasons, successful B2C campaigns typically trigger emotional reactions or responses, while B2B campaigns focus on offering immediate value. Understanding these differences and making the appropriate changes to your B2C marketing strategy will improve your outcomes.
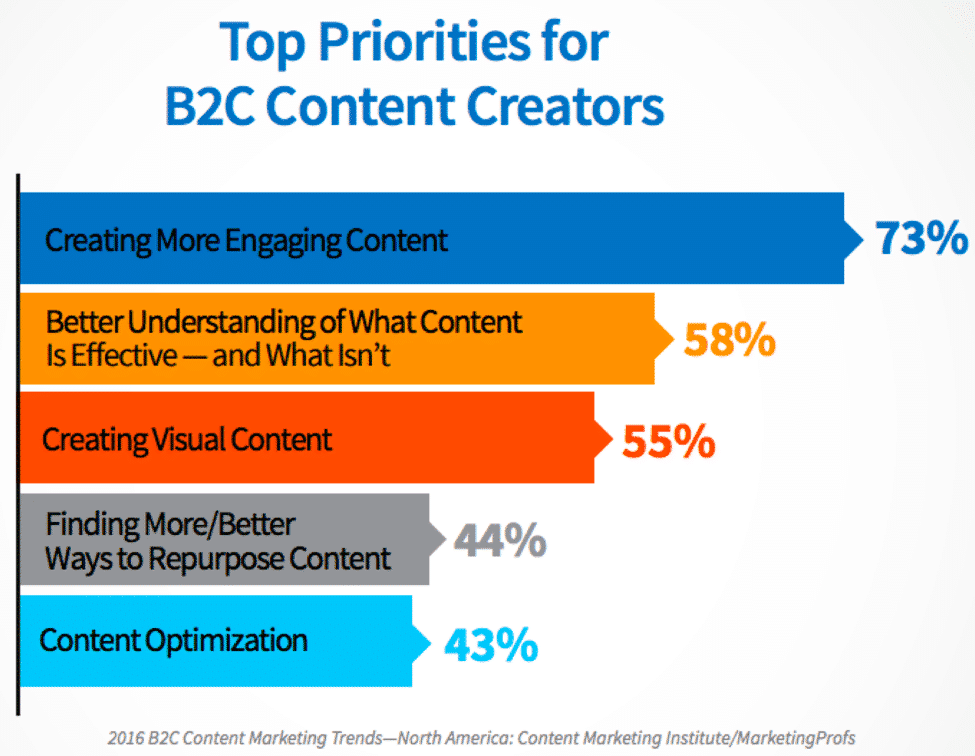
Businesses that focus on B2C marketing observe trends closely, research their customers’ purchase habits, and closely monitor their competitors’ tactics, as it’s critical to know the challenges — and understand how to break through all the noise to find success. A recent benchmark report from The Content Marketing Institute examined what B2C marketers consider to be top priorities:
Biggest Challenges of B2C Marketing
The world of consumer-driven marketing moves at an astonishing pace.
So, despite being able to capitalize on impulse and emotion — as opposed to the purely value-driven foundations of B2B — B2C marketing still faces a core set of challenges:
Adjusting to Changing Customer Behaviors
AI. Omnichannel marketing. Unlimited access to the internet in the palm of your hand. Over the last 5 years, technology has forever changed the way that customers engage with your brand and shop online. Not only do they have more control than ever before, but they also have higher expectations, demanding a better experience from the brands they engage with.
Amidst this constant change, one thing remains clear:
If you want to keep your customers coming back to your brand, you need to deliver the relevant, flexible experiences that they demand.
You need to engage customers, not interrupt them, and meet them where they’re spending their time online with personalized content that’s relevant to their interests and shopping habits. You also need to be there, when they need you, to offer tailored, effective support.
The research exists to back this up:
- 44% of respondents cited “excellent customer service” as the main reason they stay loyal to a brand (SAP Emarsys Customer Loyalty Index 2023)
- 66% of consumers remain loyal and frequently purchase from a brand due to personalized, frequent, and relevant communications. (SAP Emarsys Customer Loyalty Index 2023)
- If their experience expectations aren’t met, 52% of customers will try their luck with a new brand. (SAP Emarsys Customer Loyalty Index 2023)
- 90% of consumers expect consistent interactions across any channel. (Forbes)
Related Content: The Definitive Guide to Customer Engagement
Additionally, most consumers today are predisposed to expect all brands to treat them as well as their favorite brand. So, as brands scramble to deliver better and better experiences, the bar for what constitutes a “good experience” will keep rising — and behaviors will keep changing.
Staying on Top of Evolving Trends & Market Changes
Driven by impulse and emotion, the B2C market moves fast — and staying on top of those changes can be a challenge for many brands. However, if you want to stay ahead in a crowded market packed with competitors fighting for your customers’ attention, you need to be ready to adapt.
When your customers are hit with hundreds of ads on a daily basis, static marketing campaigns aren’t enough to deliver a stand-out customer experience.
Fortunately, there are a number of tactics you can employ to deliver meet the continually rising bar of customer expectations:
- Leverage email marketing automations to send relevant, personalized content in real-time to your customers.
- Connect customer support to your marketing mix to help them provide a tailored service that quickly resolves queries and provides customers with a standout support experience.
- Connect in-store to online by integrating Point of Sale with your digital channels, enabling you to continue the customer journey even when they’ve left the store.
- Monitor competitors and relevant hashtags using a social media platform like Hootsuite or a competitor monitoring tool like SEMRush.
- Create a Google Alert to receive push notifications for key movements within your niche.
- Use a news aggregator like Pocket to collate key competitor events and trends.
By keeping your finger on the pulse of your industry and updating your marketing strategy to improve your customer experience, you’ll continue to meet customer expectations and stay one step ahead of your competitors.
Selecting the Most Effective Channels
Your customers are everywhere. One moment, they’re crossing the threshold of your store. The next, they’re cross-referencing prices online to find the best deal, visiting your website, and leaving your store without completing a purchase.
This is set against a backdrop of ever-changing platforms and surprise algorithm updates which directly impact how your content is displayed and consumed.
So, this begs the question – when your audience is everywhere, and the platforms are constantly changing, how do you know where to focus your presence?
To effectively navigate the challenges of the complex B2C marketing landscape as a marketer, you need to adopt a strategic, agile approach. This involves keeping your finger on the pulse of platform updates, unlocking your customer data so you can deliver personalized content with automations, and, as always, listening to your customers.
You can simplify this process with a customer engagement platform like Emarsys. With this, you can connect your online and offline marketing channels. You’ll create a marketing ecosystem where your audience receives a consistent brand experience no matter where they choose to engage.
Dealing with Data Overload
Customer data is generated at every touch point and interaction, from every customer, web visitor, or prospect you’re trying to reach.
Many B2C marketers believe this is the most significant challenge today — keeping up and making sense of all this data, then using it to draw insights and inform your marketing at scale.
This process is nearly impossible to achieve manually.
New technologies can help you by automating the process of collecting, mining, analyzing, and leveraging data. These include:
- Customer data platforms to help store and manage all customer information you’re collecting.
- Machine learning to help algorithms self-learn, without the need for manual updates.
- Artificial intelligence marketing to help you scale the process of personalization.
With so much data at hand, it’s easy for siloes to crop up, and without unified data, getting a holistic view of channel and campaign performance is a tough task. However, customer data is also your greatest asset and is the gasoline which fuels your B2C machine. Dedicating resources to breaking down silos is a worthy investment.
By leveraging customer engagement platforms and machine learning to put your data to work, you can deliver on your customers’ expectations of personalized experiences, without compromising on efficiency.
See how Emarsys empowers marketers to execute simple, single-channel campaigns, or create sophisticated, cross-channel journeys at scale.
Designing an Effective B2C Marketing Strategy
Wondering how to create a B2C marketing strategy for your business? It starts by building a real emotional connection with your customers, a fundamental step in turning casual browsers into loyal buyers. In order to build these connections, however, you first need to understand who your customers are. What are their wants and needs? What are their product and shopping preferences? What pain points do they have that your products or services solve?
Once you have this persona mapped out, you can get to work creating content that resonates with your customer. By utilizing a mixture of digital channels, from social media to email, you’ll then be able to reach your customers where they’re already spending their time. Focus on creating content that’s relevant to their interests and needs, and personalized using the data you have, and you’ll help to cut through the noise of your competitors, build engagement, and drive those all important purchases.
Successful B2C Case Studies
To achieve success as a B2C marketer, it’s important that you focus on reaching your consumers at the most appropriate time, while delivering perfectly tailored messages that ensure conversion and retention.
Here’s a look at five ways your B2C marketing efforts will be boosted by focusing on personalization and creating one-to-one interactions.
1. Levi’s found the right fit to improve their repurchase rate

Strategic goal: Levi’s Brazil aimed to enhance customer retention and repurchase rates, moving customers away from price sensitivity. The challenges included automating personalized campaigns at scale, integrating online and offline data, operating with a small team, and deepening their understanding of customer insights.
The strategy: To address these challenges, Levi’s Brazil partnered with SAP Emarsys and Driven.CX. This partnership allowed them to maximize their use of customer data, improve their understanding of customer behavior, and enhance the personalization and automation of their marketing efforts. They implemented strategies such as welcome emails, abandoned cart reminders, back-in-stock notifications, and price drop alerts.
Impact:
- +30% of results share attributed to Emarsys implementation
- +32% in revenue generation
- +7% increase average order value in 5 months
- +15,000 customers with repurchase and engagement tactics
2. Petco’s strategy keeps pet lovers coming back

Problem: Petco Mexico wanted to deliver a seamless omnichannel customer experience that integrated online and offline data but struggled due to the limitations of their previous platform, Mailchimp, which couldn’t scale with their growing business. They also needed to automate personalized campaigns across multiple channels despite having a small team. They needed a robust solution that could support their high volume of customers and deliver highly personalized engagements effectively.
Solution: With support from the Emarsys team, Petco reimagined their email programs and connected their key marketing channels, such as email, web, digital ads, and mobile apps, into a cohesive omnichannel customer experience. They also linked their loyalty program, which accounts for 92% of their purchases, into this integrated system. The solution enabled Petco to maximize their marketing technology investment and better understand their customers through advanced analytics and personalized, data-driven engagements.
Impact:
- +20% increase in revenue from active customers within 90 days
- ~300X return on ad spend
- 15% increase in won-back customers
- 31% increase in overall revenue
- +40,000 new monthly users
- 500,000 average monthly users
Future Trends in B2C Marketing
In B2C marketing, today’s innovations could be tomorrow’s table stakes. Let’s take a look at some of the upcoming trends shaping the future of B2C marketing:
Voice search optimization
Voice-enabled virtual assistants like Siri and Alexa are getting more and more popular, and they aren’t going away. As a result, voice search is becoming increasingly important for B2C marketers. Your customers will increasingly turn to voice search to get quick and convenient answers to their queries, so if you can optimize your content for those queries, you can significantly enhance your brand’s visibility.
Optimizing your content for voice search starts by understanding the natural language queries consumers use and integrating those into your website and content. For example, instead of “best air fryer 2023”, your customers will likely search for something like “what’s the best air fryer right now?”. By focusing on these long-tail, question-phrased keywords, you’ll prepare yourself for a new search landscape where voice is set to play a pivotal role.
Social commerce
Social media was once a platform for discovery and education. Now, it’s a vibrant shopping destination where customers can complete their purchase without leaving the app. With new e-commerce features like shoppable posts, in-app checkout and live shopping experiences, social media channels are fast becoming platforms not just for advertising, but for direct sales.
The seamless integration of e-commerce and social media is opening up new opportunities for brands, creating fresh revenue streams. If you want to tap into them, you need to pivot your strategy and start creating engaging, high-quality content that leverages social commerce features and drives customers towards on-platform purchases.
Subscription-based models
Subscriptions are convenience, and when it comes to e-commerce, convenience is king. Subscription-based business models are expected to continue their rise in popularity, as they deliver convenience, flexibility, and personalized experiences to consumers.
With automatic renewals and deliveries and tailorable, personalized products selections, subscription models enhance the customer experience by simplifying purchase decisions and catering to individual preferences and needs.
The challenge here lies in maintaining a clear value proposition so customers keep their subscription, but if you can tackle this, subscriptions will be a powerful strategy for driving retention and customer lifetime value. So, get your data in order, build a clear understanding of your customers’ wants and needs, and create your own customizable subscription offering.
Hyper-local targeting
Your next sale could be just around the corner. No, really, it could be – and geotargeting can help you secure it. Recent advances in location-based technologies and geotargeting are revolutionizing how B2C marketers attract and convert customers, enabling them to deliver highly targeted, relevant messaging to consumers based on their precise location, preferences and behaviors.
Got a physical retail location? Actively drive nearby customers to your store with personalized offers and push notifications. Run a clothing company? Tailor your ads to the weather in different locations. Personalization is key to not making geotargeting feel intrusive. Make sure your geotargeting campaigns are relevant to each customer, and use it as a tool to build trust.
Influencer marketing
We all know just how powerful influencer marketing and UGC can be. However, identifying, connecting and agreeing terms with influencers has always been a tricky, manual, time-consuming process for brands. As a result, influencer marketing was typically an activity left for bigger brands with larger budgets.
This is where influencer marketing platforms have come in. By utilizing advanced algorithms, these platforms can match influencers based on niche, demographic data, engagement rates, and past collaboration success. This not only streamlines the search and vetting process, but also helps to drive campaign performance by making sure your brand and your potential influencer are a good fit.
As a result, these platforms are making influencer marketing ever more accessible and efficient, enabling smaller brands to leverage this strategy to increase visibility, build trust, and drive sales.
Unleash the Power of Omnichannel Customer Engagement in Your B2C Marketing
With customers time-poor, option-rich, and more demanding than ever, personalization is the future of B2C marketing. But with multiple channels, campaigns, and touchpoints, creating automations that effectively deliver personalized content can be a challenge for B2C brands.
Emarsys can help. Our omnichannel customer engagement platform helps B2C brands create and deploy 1:1 personalized B2C marketing automations that trigger in real-time across multiple channels all within one platform.
See for yourself in just 3 minutes how Emarsys drives omnichannel 1:1 customer engagement.
Additional Resources: